Sign up to unlock more features
- Save this deck to your account
- Study flashcards with spaced repetition
- Export to Anki (.apkg) or PDF
- Process documents up to 100 pages
- Images extracted from PDFs and documents
- Better text extraction from your PDFs and documents
- Better flashcards with our more advanced AI model
Flashcards in this deck (29)
-
What is the difference between packet sniffing and packet spoofing?
- Packet sniffing: captures network traffic using tools/techniques like pcap, raw sockets, or BPF
- Packet spoofing: forges packet headers (e.g., IP, ICMP, UDP) by constructing raw packets or using Scapy
network security -
What is the primary difference between packet sniffing and packet spoofing?
- Packet sniffing: captures network traffic (pcap/raw sockets/BPF)
- Packet spoofing: forges packet headers (IP/ICMP/UDP) using raw packets or Scapy
networking security sniffing spoofing -
How does a NIC decide to copy a received Ethernet frame into a buffer for dispatch to user-space?
If the destination address in the frame header matches the NIC (or filter), the frame is copied into a ring buffer and dispatched to user-space programs.
network nic packet-reception -
What is promiscuous mode on a network interface card (NIC)?
- The NIC passes every received frame to the kernel
- A registered sniffer can see all packets
- Enabling usually requires elevated privilege (root)
networking promiscuous -
How does Wi‑Fi monitor mode affect what 802.11 frames a card can capture?
- Monitor mode captures 802.11 frames only on the channel the card is listening to; due to channels and interference, the card may miss frames on other channels.
networking wifi sniffing -
Why should packet sniffers filter unwanted packets as early as possible?
- It prevents the system from handing all captured packets to the sniffer program, which would then discard most unwanted packets and be inefficient.
networking sniffing -
What does the BSD Packet Filter (BPF) allow a user program to do with a socket?
- Attach a filter to the socket that tells the kernel to discard unwanted packets
 bpf kernel filtering networking
bpf kernel filtering networking -
What is packet sniffing and what are the tools that perform it called?
- Packet sniffing captures live data as they flow across a network.
- Tools that perform packet sniffing are called packet sniffers.
networking security -
What are the main high-level steps to receive UDP packets using a socket?
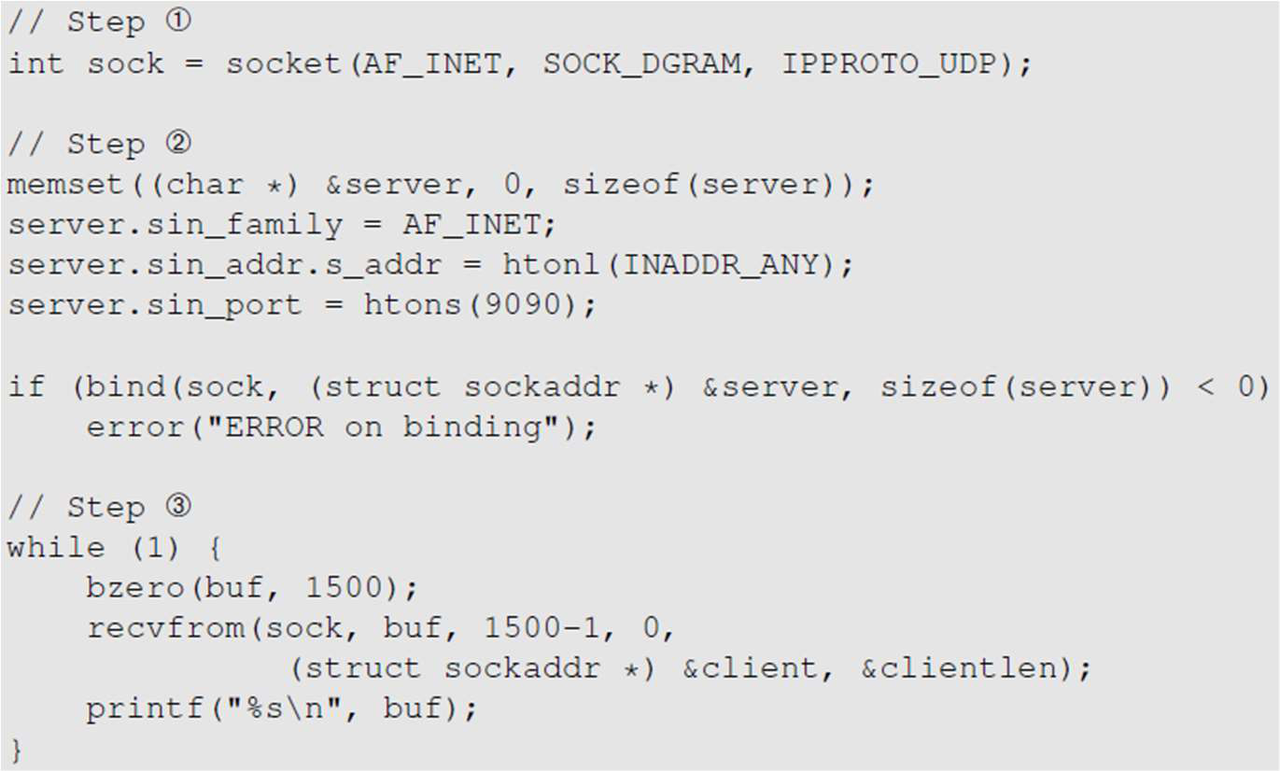
- Create a UDP socket (AF_INET, SOCK_DGRAM, IPPROTO_UDP)
- Configure server address and port then bind (INADDR_ANY, port 9090)
- Receive packets in a loop using recvfrom and process the buffer
networking udp sockets -
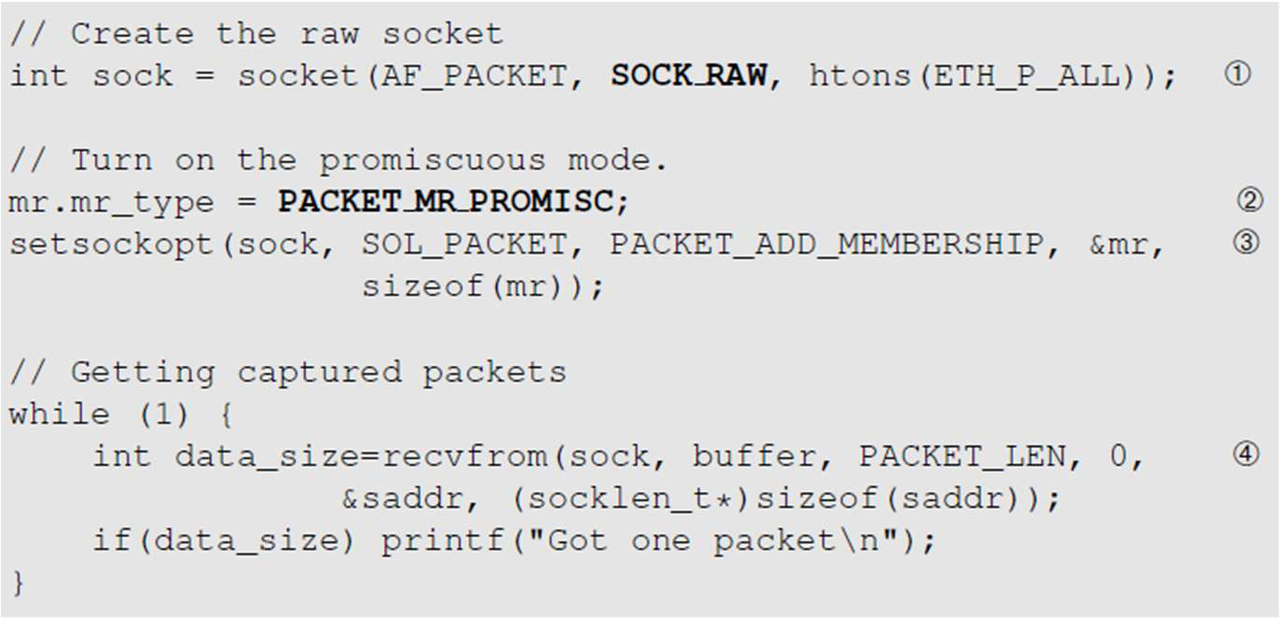
What are the high-level steps to capture packets using a raw socket for a sniffer?
- Create a raw socket: socket(AF_PACKET, SOCK_RAW, htons(ETH_P_ALL))
- Enable promiscuous mode: use PACKET_MR_PROMISC with PACKET_ADD_MEMBERSHIP via setsockopt
- Receive packets: loop calling recvfrom() to read captured packets
 networking sniffing rawsocket
networking sniffing rawsocket -
What key advantages does the PCAP library provide over using raw sockets for packet capture?
- Cross-platform standard API
- Hides OS-specific details
- Allows human-readable Boolean filtering rules
pcap networking -
What are the main steps in pcap-based packet sniffing using the pcap API?
- Open a live pcap session (e.g., pcap_open_live)
- Compile and set a BPF filter (pcap_compile, pcap_setfilter)
- Capture packets and handle them in a callback (pcap_loop and got_packet)
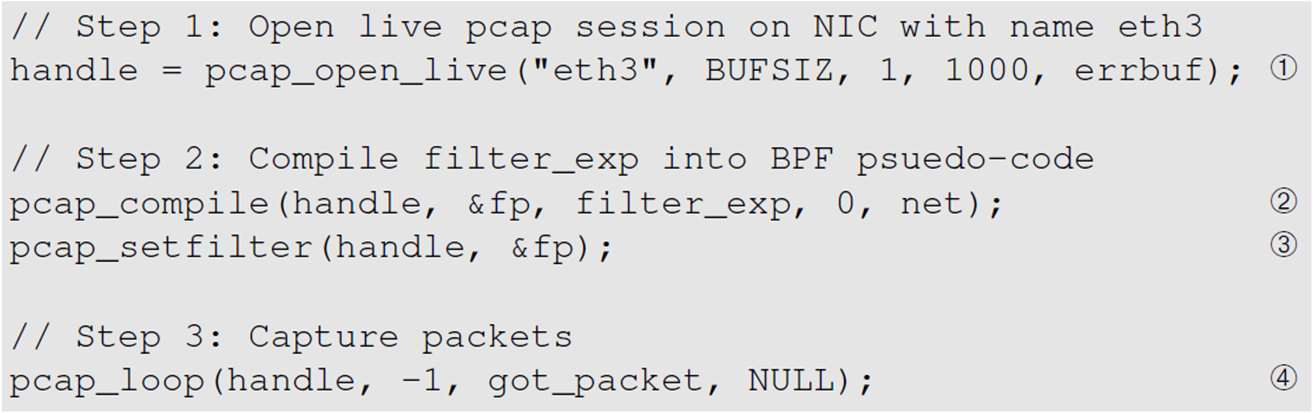 pcap sniffing bpf
pcap sniffing bpf -
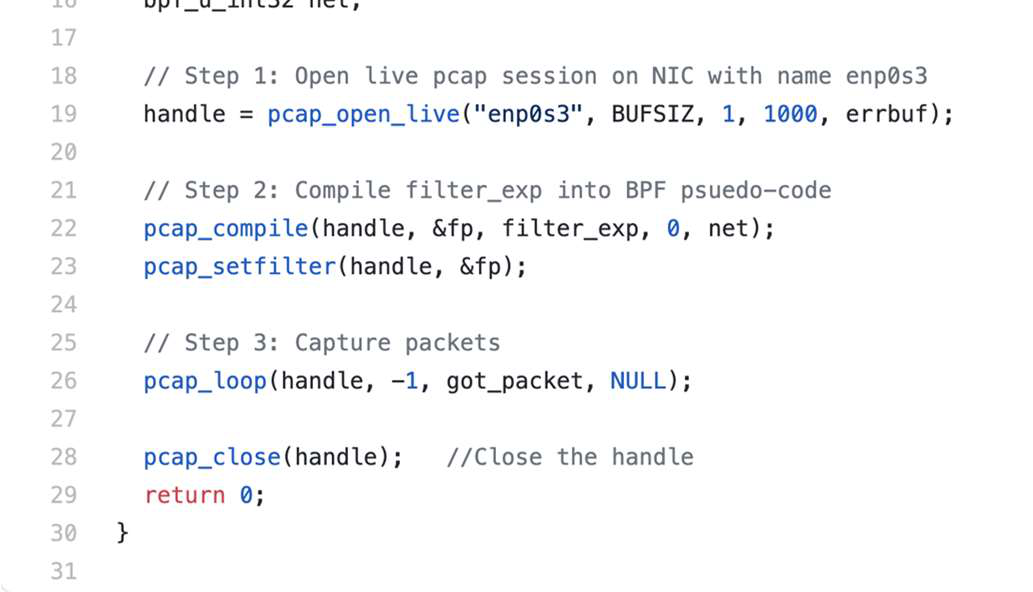
What are the main steps of the pcap packet capture workflow demonstrated by sniff.c?
- Open a live pcap session on a NIC
- Compile a filter expression into BPF
- Set the compiled filter on the handle
- Capture packets (pcap_loop) with a callback
- Close the pcap handle
 pcap sniffing bpf
pcap sniffing bpf -
networking security
-
What are the main steps shown to send a UDP packet without spoofing in the example code?
- Create a UDP socket
- Provide destination information (IP and port)
- Call sendto() with the payload and destination, then close the socket
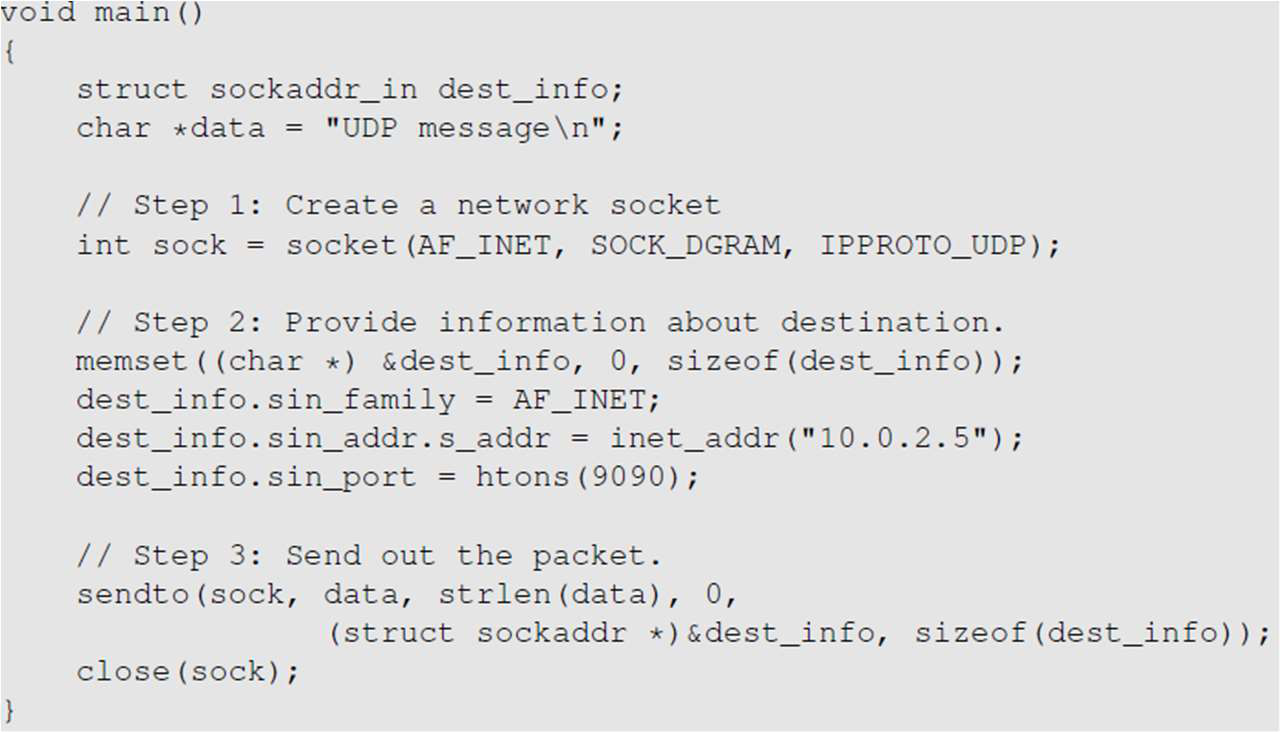 networking udp sockets
networking udp sockets -
Why use a raw socket when spoofing packets?
Because a raw socket lets you construct the entire packet in a buffer including the IP header; typical sockets have header fields (e.g., source IP, packet length) set by the OS.
networking spoofing rawsocket -
What are the key steps shown to construct an ICMP echo request (spoofed packet) in the example code?
- Find the ICMP header start and typecast to struct icmpheader
- Fill ICMP fields (set icmp_type to 8 for request)
- Set icmp_chksum = 0
- Compute and store checksum using in_cksum
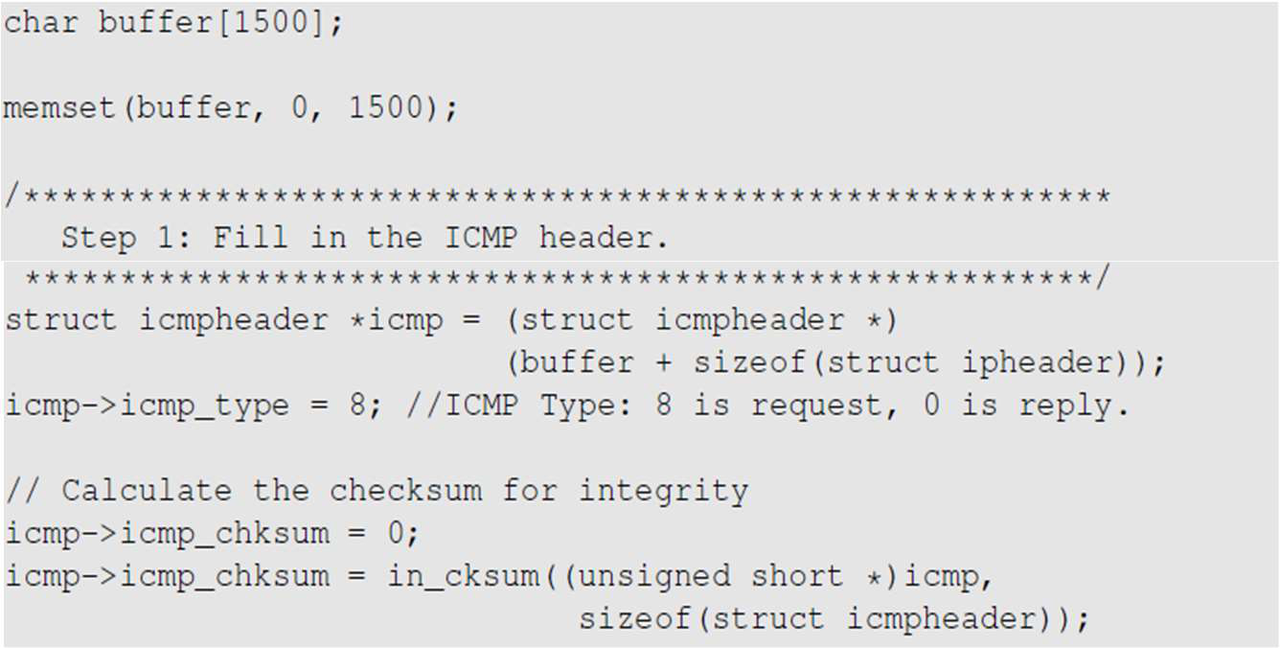 icmp spoofing networking checksum
icmp spoofing networking checksum -
In the example code for constructing a spoofed IP packet, name three IP header fields that were explicitly set.
- IP version: 4
- Source and destination IPs: 1.2.3.4 and 10.0.2.5
- Protocol: IPPROTO_ICMP
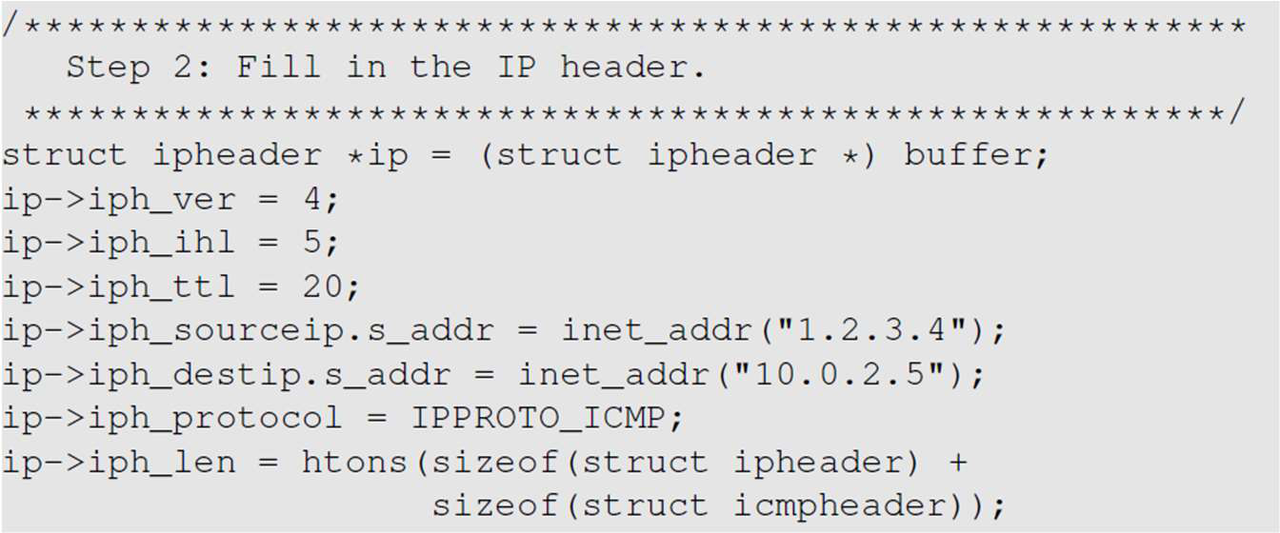 networking spoofing ip
networking spoofing ip -
When constructing spoofed UDP packets, what key element must be included that differs from spoofed IP or ICMP packets?
- Payload data
networking spoofing udp -
What are the high-level steps of a sniff-and-spoof workflow for UDP packets?
- Capture UDP packets using a PCAP API
- Copy the captured packet
- Replace the UDP data field and swap source and destination fields
- Send the spoofed reply
- (Alternative): use Scapy in Python instead of C
networking security -
In the C function shown for spoofing UDP packets, after confirming the packet's destination port is 9999, what are the two main steps performed to create the spoofed reply?
- Make a zeroed copy of the original packet into a local buffer and set newip/newudp pointers
- Construct the UDP payload by copying the spoofed message into the packet data area
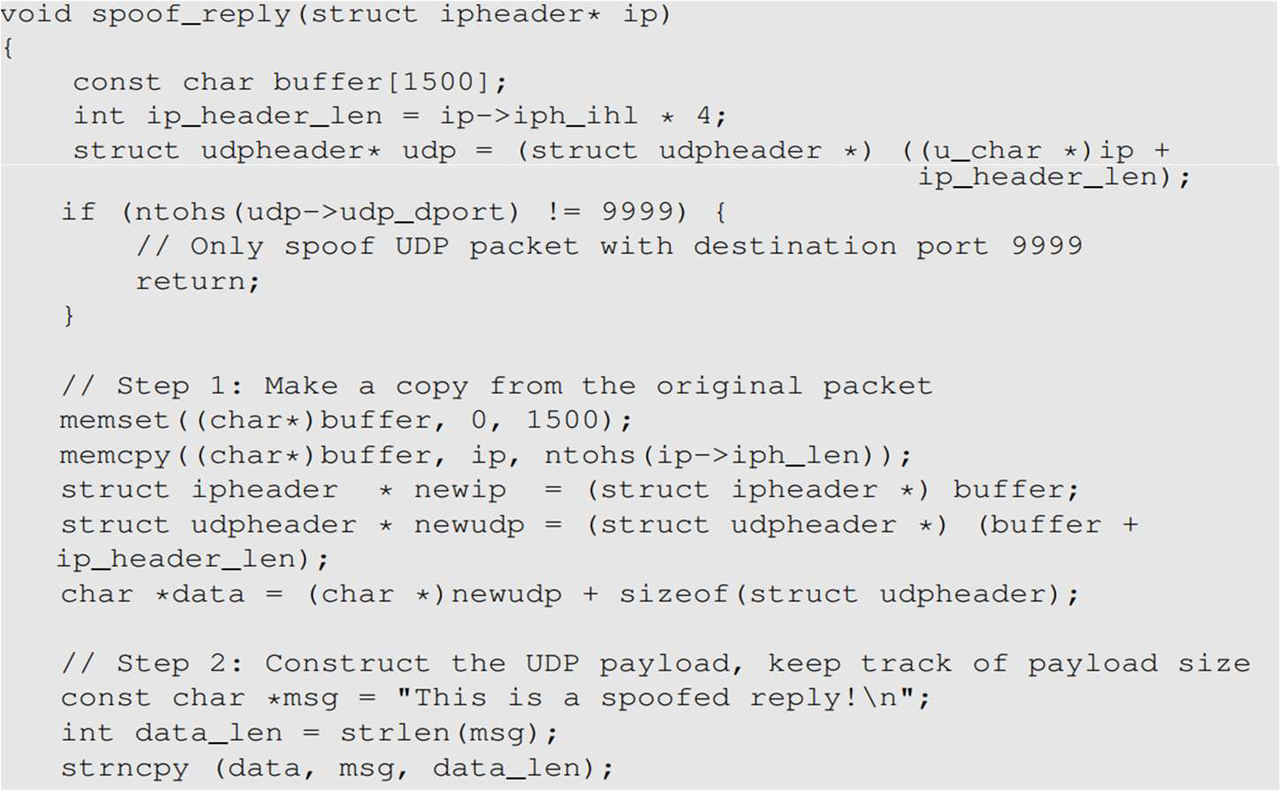 networking spoofing udp c
networking spoofing udp c -
Which UDP header fields are set when constructing the spoofed UDP packet in the code snippet?
- udp_sport set to the original packet's destination port
- udp_dport set to the original packet's source port
- udp_ulen set to htons(sizeof(struct udpheader) + data_len)
- udp_sum set to 0
networking spoofing udp -
In the Scapy script shown, which packet fields are printed for each captured ICMP packet?
- Source IP
- Destination IP
- Protocol
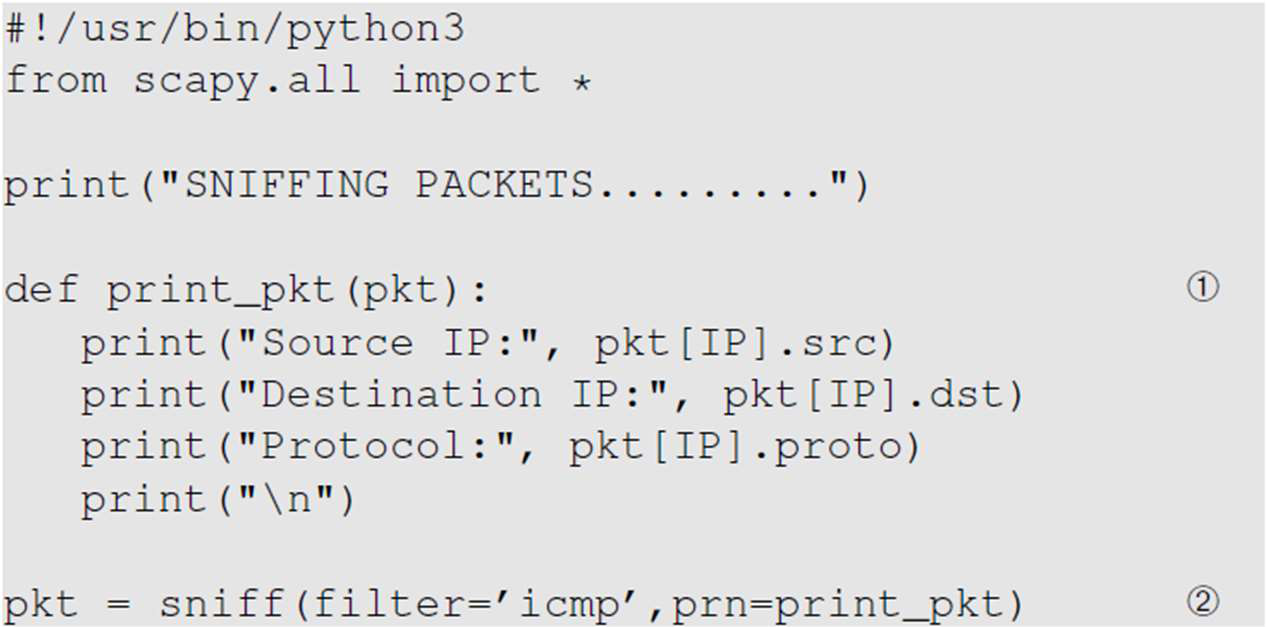 scapy sniffing icmp
scapy sniffing icmp -
In the ICMP example using Scapy, which protocol layers are combined to create the spoofed packet?
- IP layer (with spoofed src and dst addresses)
- ICMP layer
networking scapy spoofing -
In a Scapy "sniff-then-spoof" workflow for ICMP shown in the snippet, what high-level packet modifications convert an ICMP echo request into a spoofed echo reply?
- Swap the IP source and destination
- Set ICMP type to 0 (reply)
- Preserve ICMP id and seq
- Reuse the original Raw payload
- Send the newly constructed packet
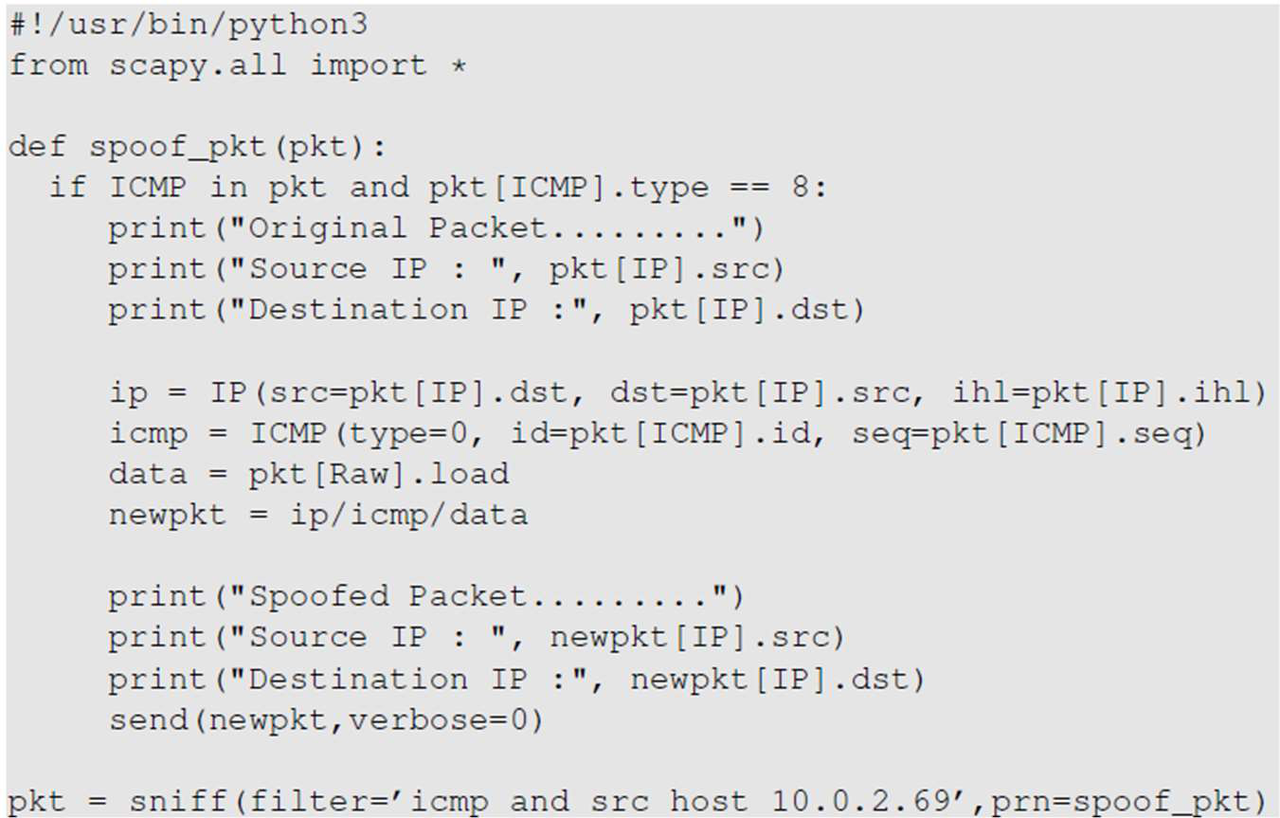 scapy icmp spoofing sniffing
scapy icmp spoofing sniffing -
What are the high-level trade-offs between using Scapy (Python) and C raw sockets for packet spoofing, and what does a hybrid approach combine?
- Scapy (Python): constructing packets is very simple; much slower than C
- C raw sockets: much faster; constructing packets is complicated
- Hybrid: use Scapy to construct packets and C to modify/send them
networking spoofing scapy c hybrid -
What is endianness and how do Little Endian and Big Endian differ in byte order?
- Endianness is the order in which a multi-byte data item is stored in memory.
- Little Endian stores the least significant byte at the lowest memory address (small end first).
- Big Endian stores the most significant byte at the lowest memory address (big end first).
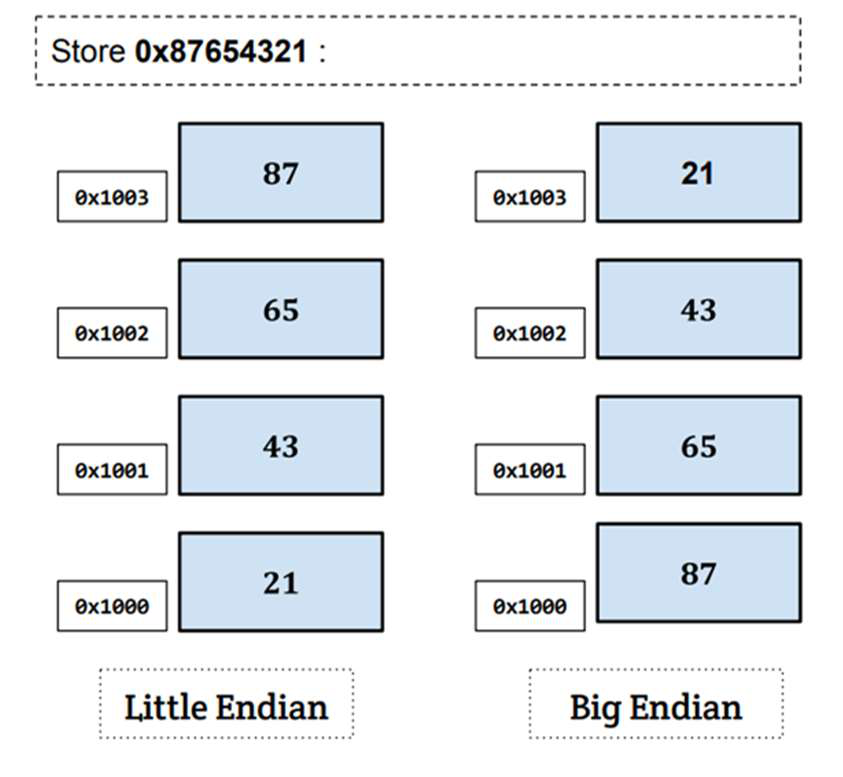 endianness networking
endianness networking -
What is 'network byte order' and which macros perform host↔network conversions?
- 'Network byte order' = big-endian
- 'htons()' and 'htonl()': convert host → network
- 'ntohs()' and 'ntohl()': convert network → host
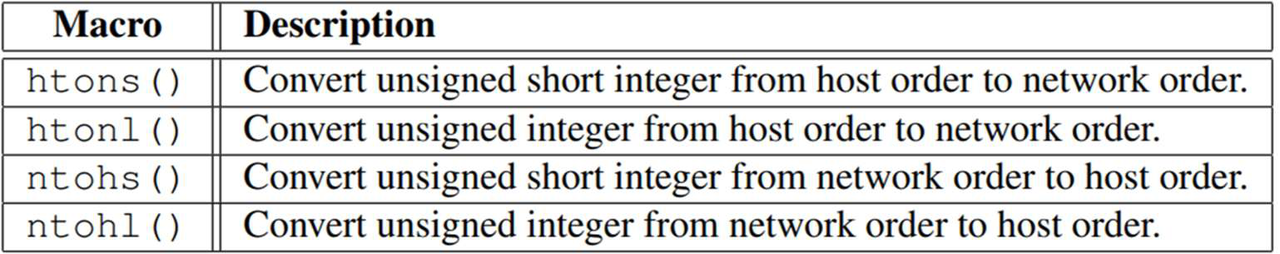 endianness networking
endianness networking -
Name three methods/tools mentioned for packet sniffing and spoofing.
- Raw sockets
- PCAP APIs
- Scapy (or a C/Scapy hybrid)
networking sniffing spoofing
Overview
- Topic: packet sniffing (capturing) and packet spoofing (forging) on IP networks.
- Focus: how packets are received, capture techniques (raw sockets, BPF/pcap), constructing spoofed packets (ICMP/UDP), and practical tools (Scapy, C raw sockets).
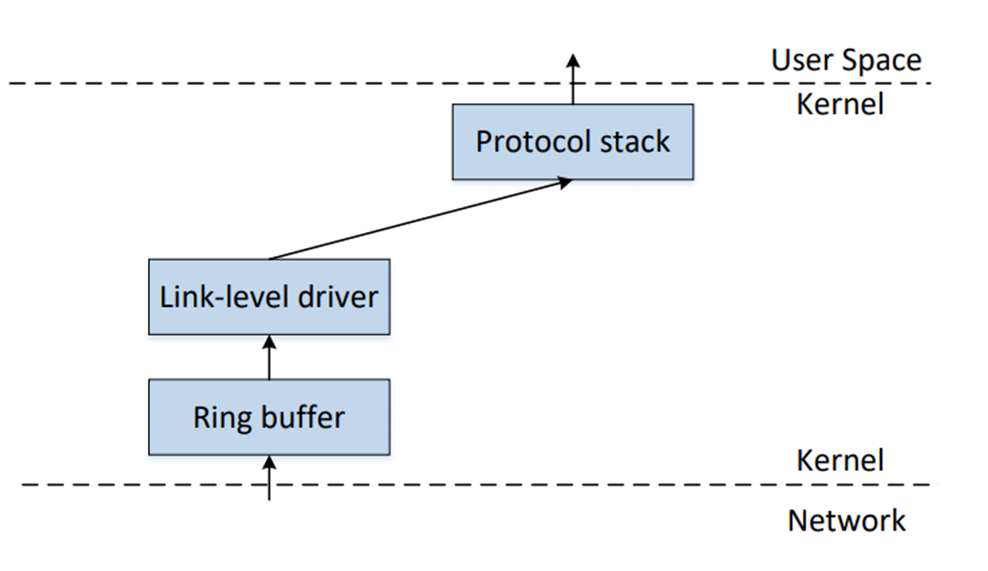
How packets are received (conceptual)
- Network Interface Card (NIC) receives frames from the physical medium and uses a MAC address to determine intended destination.
- Normally the NIC discards frames not addressed to its MAC; in promiscuous mode the NIC forwards every frame to the kernel.
- The kernel places received frames into a ring buffer and passes them up the protocol stack into sockets or user-space programs.
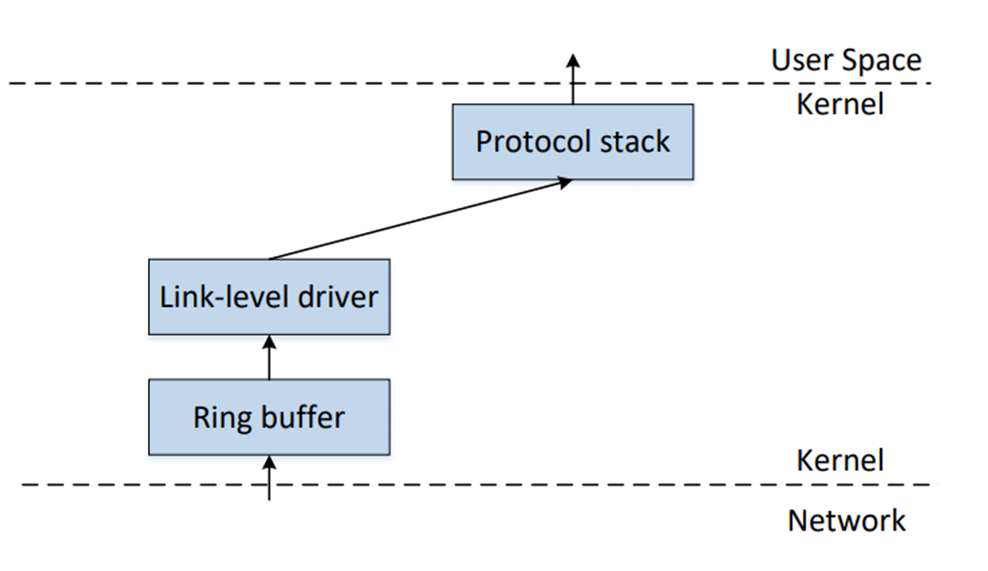 Alt: Diagram of link-level driver, ring buffer, kernel and user space.
Alt: Diagram of link-level driver, ring buffer, kernel and user space.
Promiscuous / Monitor modes
- Promiscuous mode (wired): NIC forwards all frames to kernel regardless of destination MAC, enabling full-wire capture.
- Monitor mode (wireless): Wi‑Fi cards can capture 802.11 frames on a single channel; you may miss traffic on other channels.
- Enabling these modes typically requires elevated privileges (root).
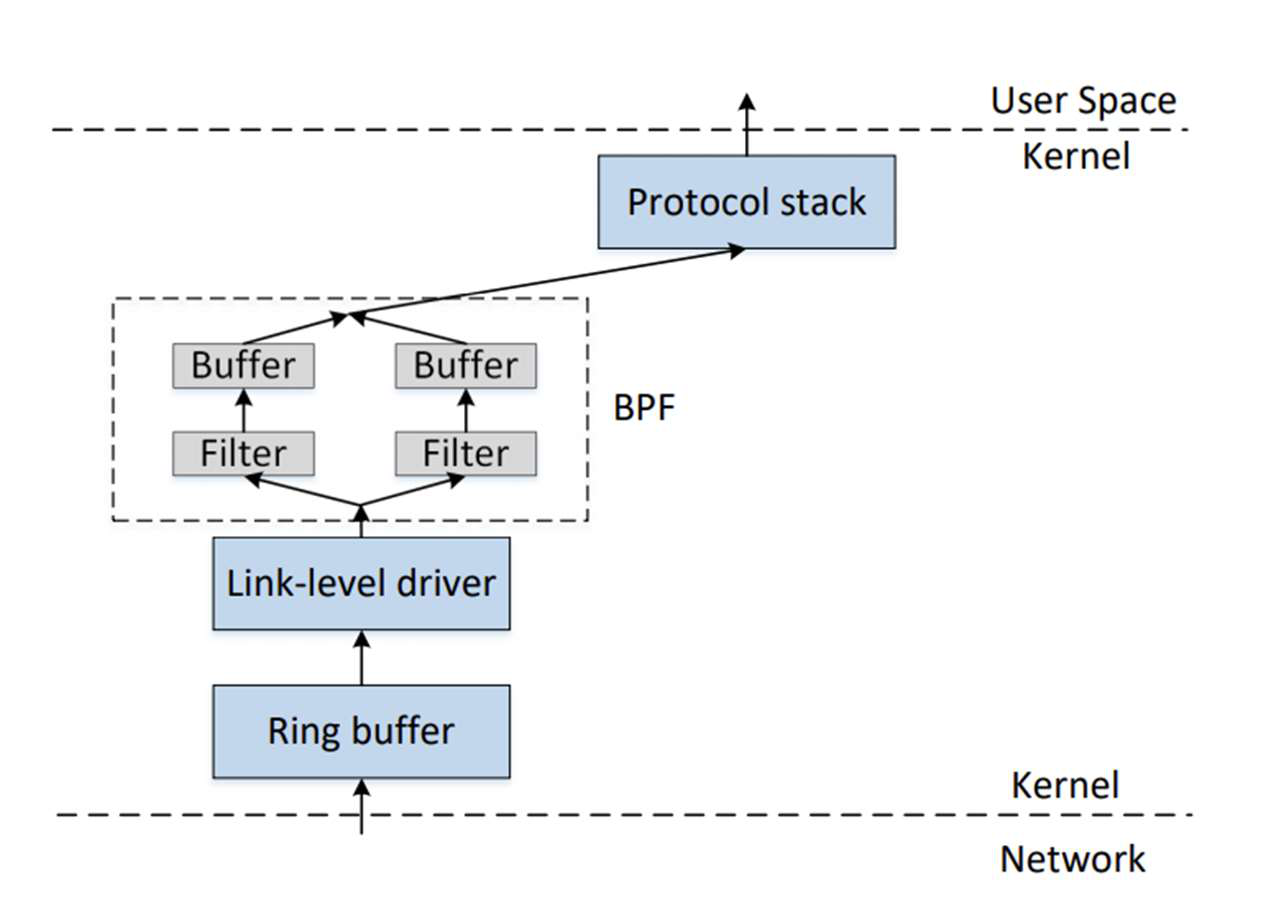
Capturing efficiently: BPF and pcap
- Giving every packet to a sniffer is expensive; better to filter early in kernel.
- BSD Packet Filter (BPF) attaches a filter to the socket so kernel discards unwanted packets (e.g., allow only port 22).
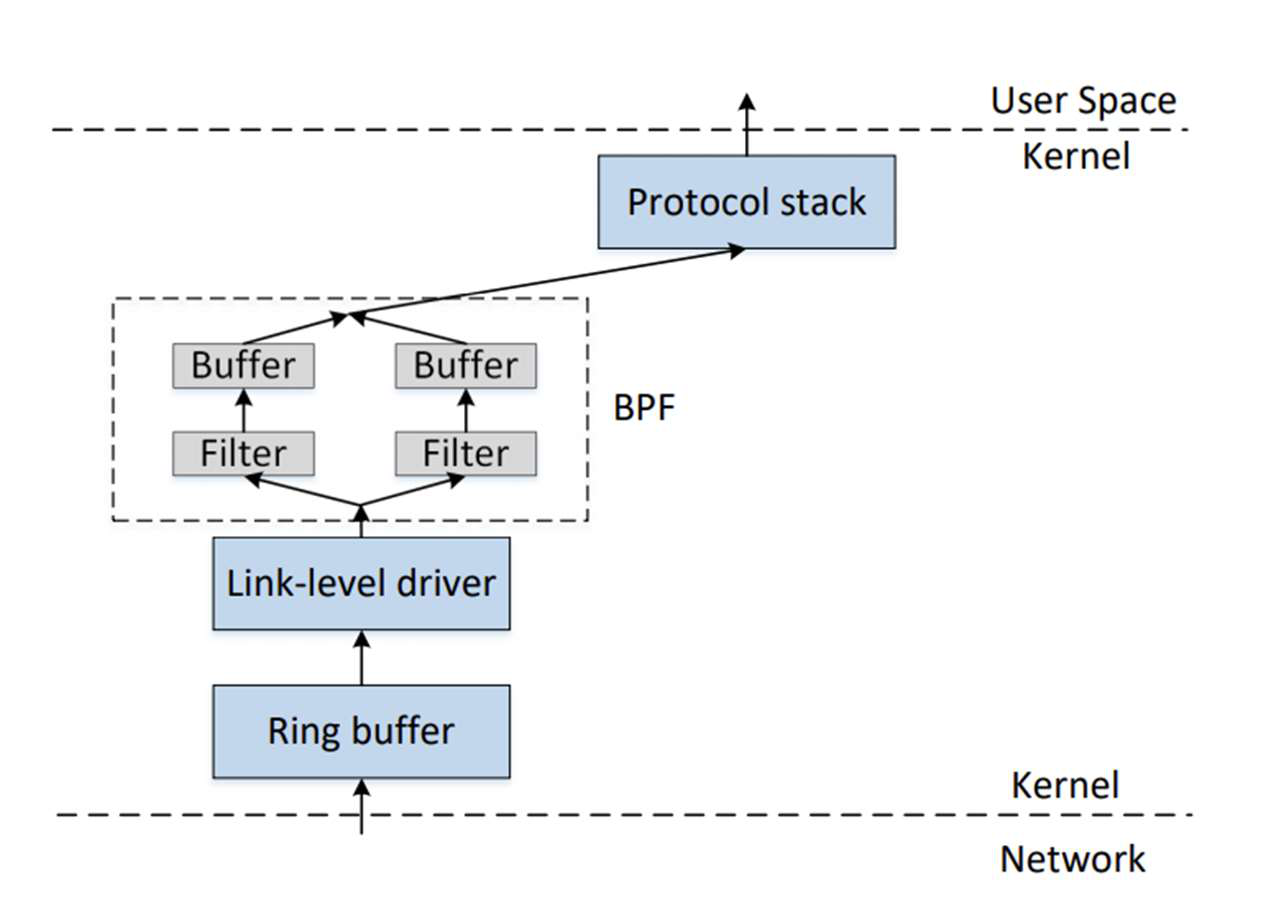 Alt: BPF flow: buffers, filters, kernel, user space.
Alt: BPF flow: buffers, filters, kernel, user space.
- pcap library (libpcap/WinPcap) provides a portable API for packet capture and filter compilation into BPF bytecode.
- Typical pcap flow: open live device, compile filter expression (e.g.,
"ip proto icmp"), set filter, then loop to receive packets.
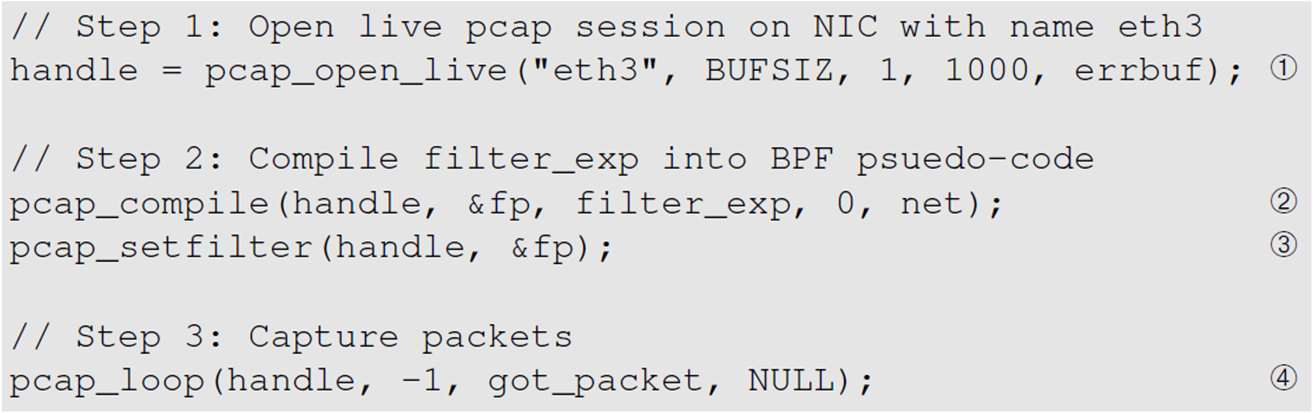 Alt: pcap_open_live, pcap_compile, pcap_loop example.
Alt: pcap_open_live, pcap_compile, pcap_loop example.
Low-level capture: raw sockets
- A raw socket receives entire link/IP packets and can be used to implement sniffers and custom senders.
- Example steps: create raw socket (e.g.,
socket(AF_PACKET, SOCK_RAW, htons(ETH_P_ALL))), enable promiscuous membership,recvfrom()loop. - Limitations: non-portable across OSes and less convenient than pcap for filters and portability.
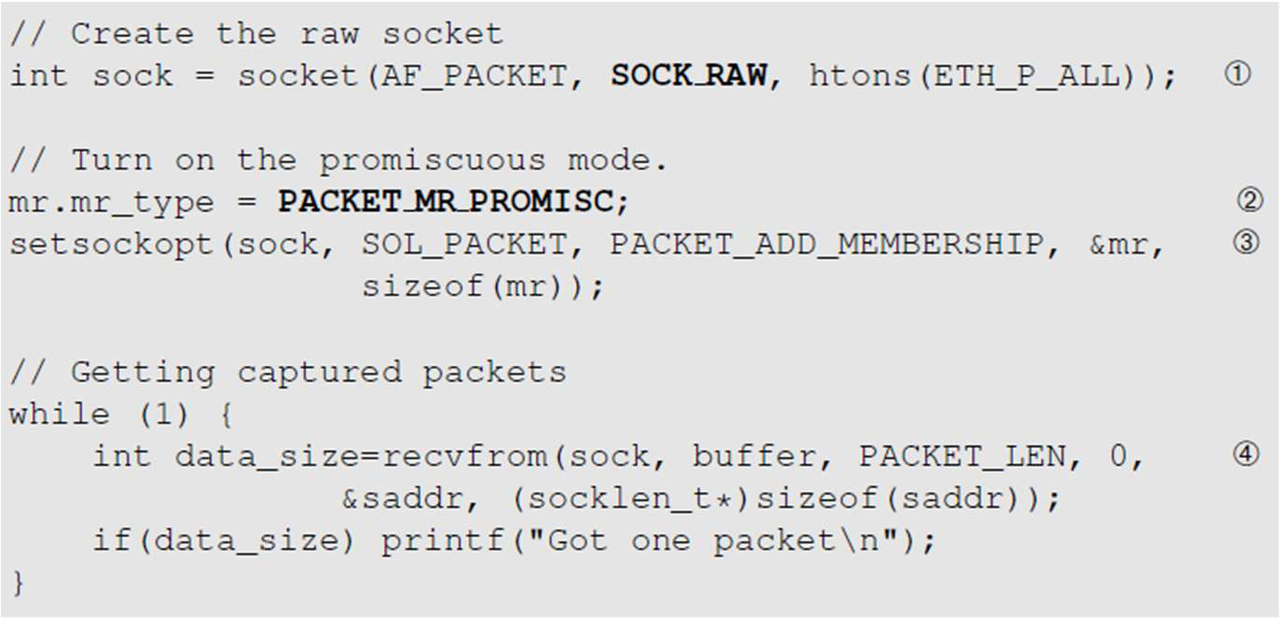 Alt: Raw socket creation and enabling promiscuous mode.
Alt: Raw socket creation and enabling promiscuous mode.
Basic sniffing examples
- UDP server style: use a normal UDP socket and
recvfrom()to see traffic directed to your host. - Raw sniffer style: use raw sockets or pcap to capture arbitrary traffic (requires root).
- Common tools built on pcap: tcpdump, Wireshark, and custom C programs.
Packet spoofing (concept)
- Packet spoofing: forging critical header fields (source IP, ports, TTL, etc.) to create crafted packets that the receiver treats as legitimate.
- Two main approaches:
- Use regular sockets to send packets (OS sets header fields — limited control).
- Use raw sockets or packet libraries to build full packets (you set IP/ICMP/UDP headers and payload).
- Root privileges are required to send forged packets.
Building spoofed packets in C (raw sockets) — key steps
- Allocate a buffer large enough for IP header + transport header + payload.
- Fill in transport header (e.g., ICMP: set type, code, compute checksum).
- Fill in IP header fields explicitly (version, IHL, TTL, protocol, source/dest addresses, total length).
- Compute any required checksums (ICMP/UDP pseudo-header checksums if needed).
-
Send using a raw IP send function or raw socket.
-
Example highlights: set
ip->iph_sourceip.s_addr = inet_addr("1.2.3.4")to spoof the source IP; seticmp->icmp_type = 8for echo request. - Constructing UDP spoofed packets is similar but includes a payload and UDP checksum handling.
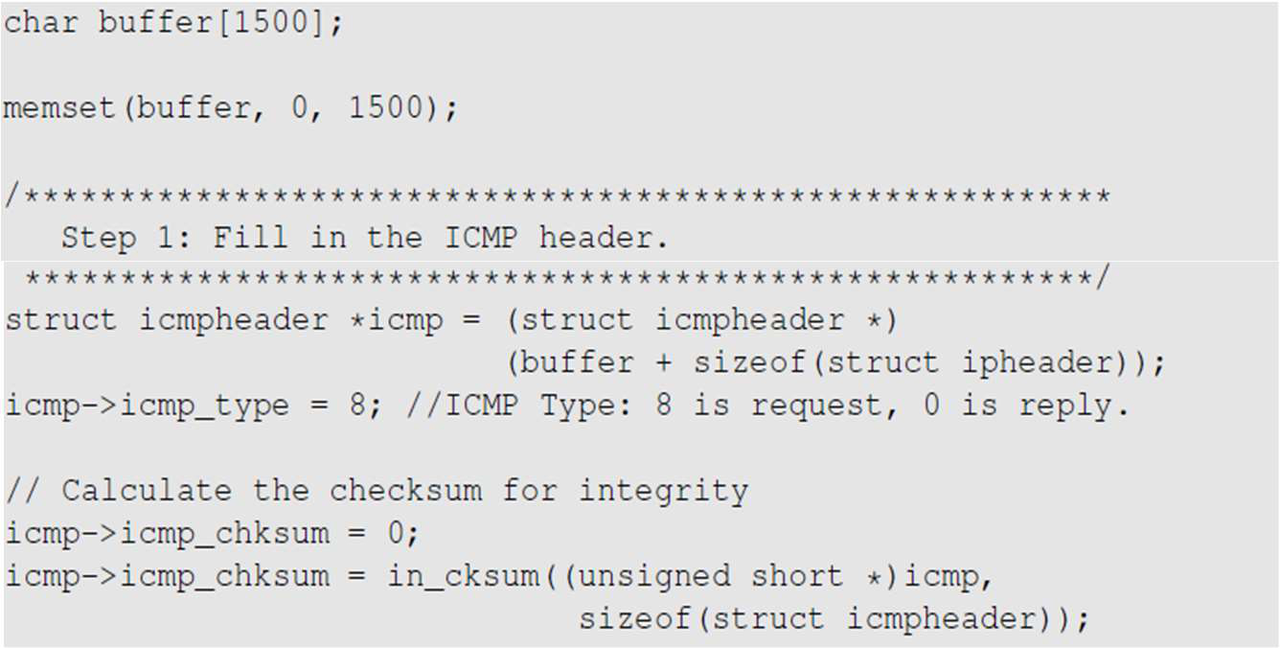 Alt: C code filling ICMP header and checksum.
Alt: C code filling ICMP header and checksum.
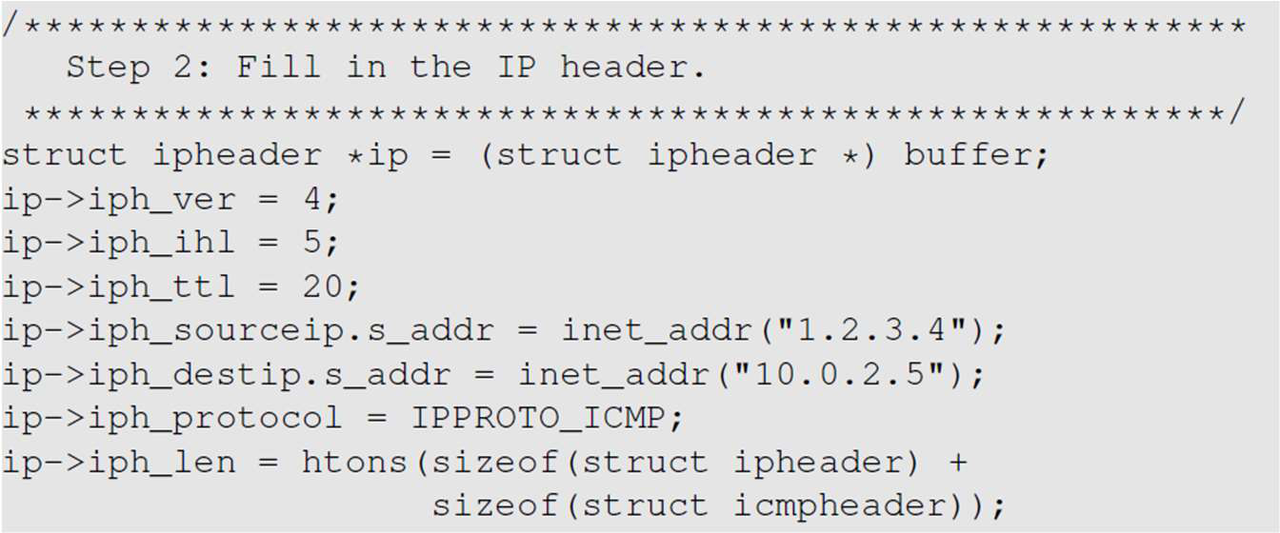 Alt: C code filling IP header fields (version, ttl, src/dst, protocol).
Alt: C code filling IP header fields (version, ttl, src/dst, protocol).
Sniff-then-spoof workflow
- Common attack/automation pattern:
- Capture an incoming packet of interest using pcap or Scapy.
- Copy relevant headers and payload metadata.
- Swap source/destination fields and replace or modify payload.
- Recompute checksums and send the forged reply.
- You can implement this in C (fast) or Python+Scapy (easy to write). A hybrid approach uses Scapy to craft and C to send at high speed.
C (example) — main points
- Copy the original IP packet into a local buffer, locate the UDP header via
ip->iph_ihl * 4, replace data and swap ports, update lengths, then send via raw send function.
Scapy (Python) — main points
- Scapy builds and sends packets with minimal code:
ip = IP(src="1.2.3.4", dst="dst");pkt = ip/UDP(sport=8888,dport=9090)/"data";send(pkt). - Scapy can also sniff (
sniff(filter='icmp',prn=func)) and reply interactively by constructing new packets from captured ones.
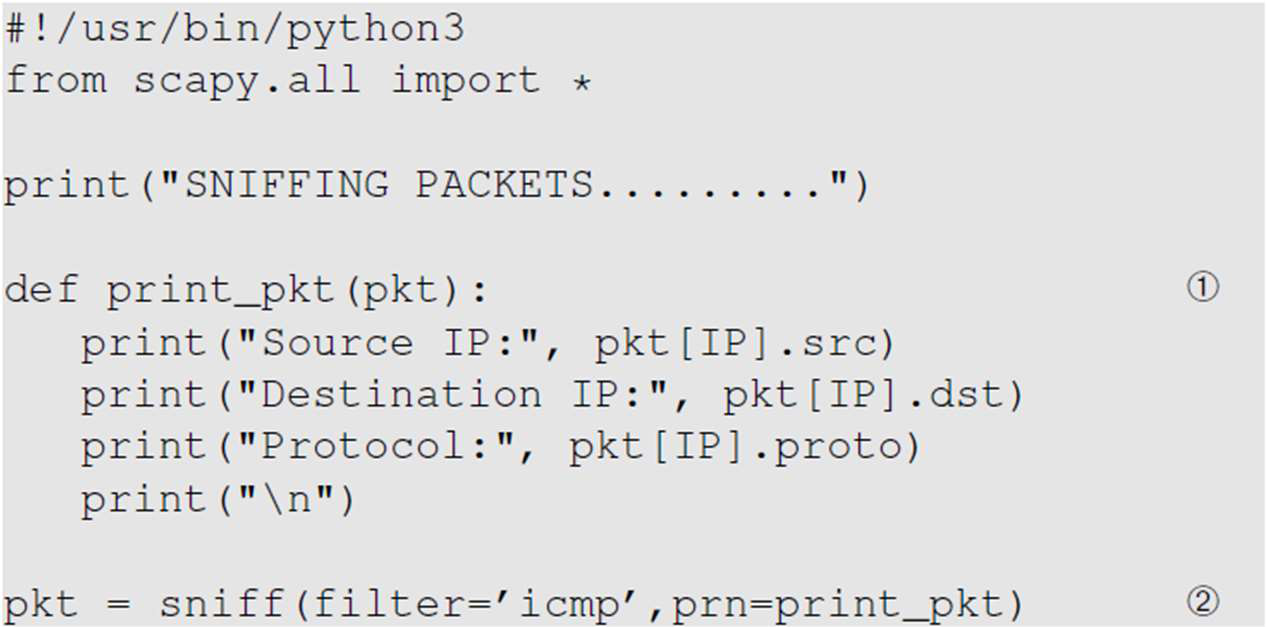 Alt: Python/Scapy snippet for sniffing ICMP packets.
Alt: Python/Scapy snippet for sniffing ICMP packets.
Tools comparison
- Scapy (Python): very simple packet construction and sniffing; slower at high rates.
- C + raw sockets: high performance and fine-grained control; code is more complex and error-prone.
- Hybrid: use Scapy to prototype packet format, then implement high-speed sender in C.
Endianness and network byte order
- Endianness: order of bytes in multi-byte values — little-endian (LSB first) vs big-endian (MSB first).
- Network byte order: agreed convention for network communication = big-endian.
- Convert between host and network order using macros:
htons()/htonl()— host to network (short / long)ntohs()/ntohl()— network to host
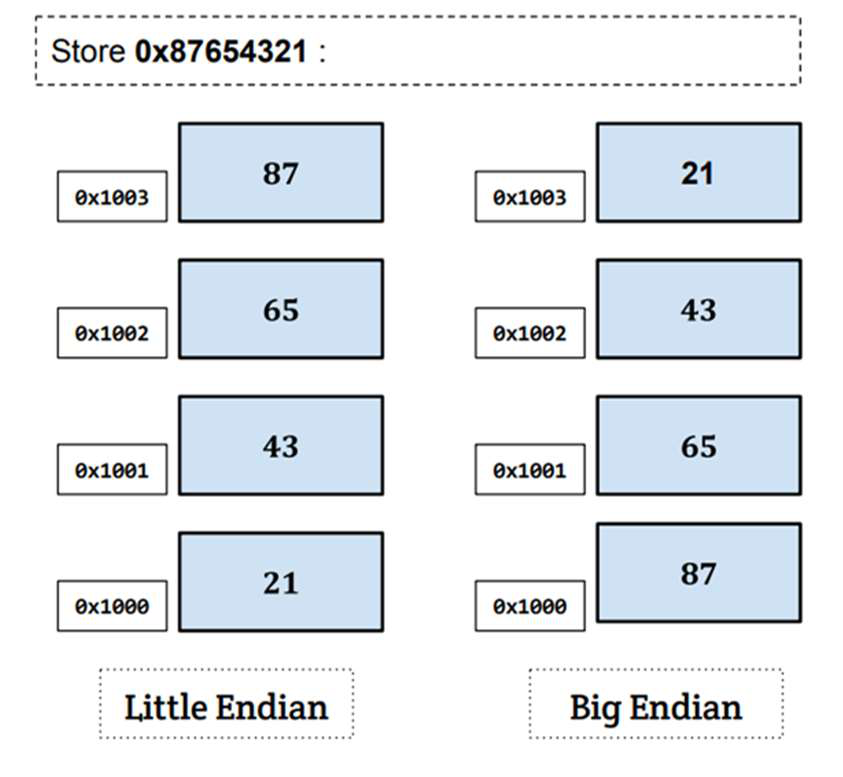 Alt: Little Endian vs Big Endian byte ordering diagram.
Alt: Little Endian vs Big Endian byte ordering diagram.
Practical notes and defenses
- Root required: capturing all traffic or forging packets typically requires root privileges; be careful and legal.
- Use of filters: always compile and set BPF filters to limit capture volume (improves performance).
- Defenses against spoofing/abuse: ingress/egress filtering, reverse path forwarding (RPF), strong authentication at the application layer (TLS), and firewalls that check packet semantics.
- Wireless caveat: monitor mode captures only one channel at a time; you may miss cross-channel traffic.
Quick checklist for implementing a sniffer/spoofer
- Choose capture method: pcap (portable) or raw socket (low-level).
- Enable promiscuous/monitor mode if needed (requires root).
- Apply BPF filters early to reduce load.
- For spoofing, build full packet (IP + transport + payload) and recompute checksums.
- Test in an isolated lab; ensure legal authorization.
One-line summary
- Packet sniffing captures network traffic (pcap/BPF/raw sockets); spoofing forges packet headers (ICMP/UDP) by building raw packets or using Scapy.